All articles containing the tag [
Problems
]-
Monitoring Indicators And Abnormal Alarm Configuration Suggestions For Hong Kong Cn2 Large-bandwidth Vps
for hong kong cn2 large-bandwidth vps, this article introduces key monitoring indicators, reasonable thresholds and alarm strategies, deployment and alarm channel recommendations to help improve availability and reduce false alarms.
hong kong cn2 large bandwidth vps monitoring indicators abnormal alarms bandwidth monitoring delay packet loss alarms -
Where Is The Korean Server Of Warcraft Asia To Teach You How To Use Routing And Accelerators To Reduce Ping?
this article introduces the location of the world of warcraft asia server in south korea, and teaches you practical techniques to reduce ping through the combination of router settings and game accelerators, including route optimization, accelerator selection and testing methods.
warcraft asian server korean server routing accelerator ping reduce ping game acceleration delay optimization -
Instructions For Using Tools And Key Indicators To Detect The Quality Of Us Vps Telecom Nodes
this article introduces vps/node quality detection tools and key performance indicators for us telecommunications networks, including actual test cases, server configuration examples and data tables to facilitate engineers to locate and optimize the network.
us vps node detection tool delay packet loss bandwidth iperf3mtrtraceroute -
Countermeasures And Alternatives When Japan’s Native Ip Login Entrance Changes Frequently
when japan's native ip login entrance changes frequently, this article starts from five issues: cause, impact, monitoring, countermeasures and alternatives, and provides actionable technical and operation and maintenance suggestions to help quickly restore a stable login experience.
japanese native ip login entrance frequent changes countermeasures alternatives -
Xiaomi 4 Japan Serverless Problems Encountered By Overseas Users Returning To China And Their Solutions
this article analyzes the causes of the "serverless" problem encountered by overseas users returning to china when using xiaomi 4 in japan and gives feasible solutions, involving technical suggestions such as dns, vps, hosting, domain names, cdn and high-defense ddos, and recommends purchasing service channels.
xiaomi 4 japan serverless server vps host domain name technology cdn high-defense ddos dexun telecom -
Analysis Of Advantages Of Cn2 Computer Room In Los Angeles, Usa And Practice Of Cross-border Access Acceleration
this article evaluates in detail the network architecture, latency and packet loss performance of the cn2 computer room in los angeles, usa, and gives practical cross-border access acceleration practices and cost comparison suggestions to help enterprises choose the best cost-effective los angeles computer room solution.
los angeles cn2 computer room cn2 cross-border access acceleration los angeles computer room computer room review low-latency network bgp acceleration -
How To Bind Accounts And Retain Progress After Logging In To The Lol Mobile Game Singapore Server?
teach you in detail how to log into the lol mobile game singapore server, bind your account and retain your progress. it includes practical steps such as android/ios download, vpn settings, riot account binding, email verification, device migration, and contact customer service for recovery progress.
lol mobile game singapore server login bind account retain progress wildrift account binding progress backup -
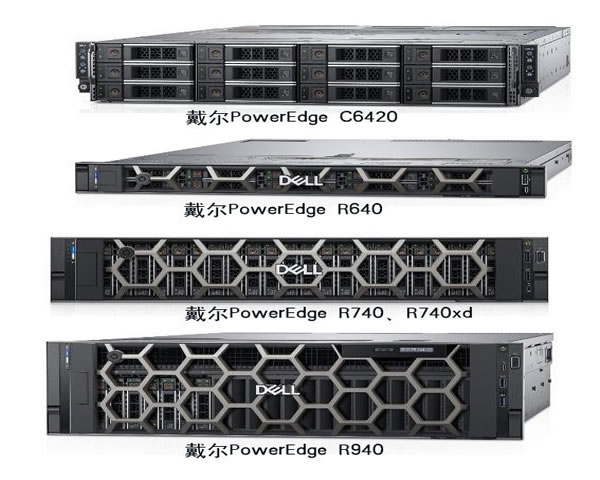
Malaysian Server Board Model Differences And Adaptation Suggested Buying Guide
this article compares the differences between common server motherboard models in detail, gives adaptation and purchasing suggestions for deploying web, database, virtualization and cdn in malaysian computer rooms, and includes real cases and configuration data examples.
malaysia server motherboard model difference adaptation buying guide vps host cdnddos defense -
Practical Cloud Desktop Migration Cloud Computer Malaysia Server Data Protection And Identity Authentication Guide
a practical guide to cloud desktop migration for enterprises, focusing on data protection and identity authentication strategies when deploying servers in malaysia, covering assessment, selection, implementation and compliance points, and providing actionable steps and best practices.
cloud desktop migration cloud computer malaysian server data protection identity authentication cloud desktop cloud migration security